- Afhalen na 1 uur in een winkel met voorraad
- Gratis thuislevering in België vanaf € 30
- Ruim aanbod met 7 miljoen producten
- Afhalen na 1 uur in een winkel met voorraad
- Gratis thuislevering in België vanaf € 30
- Ruim aanbod met 7 miljoen producten
Zoeken
Boeken geschreven door Mark Hayward
-
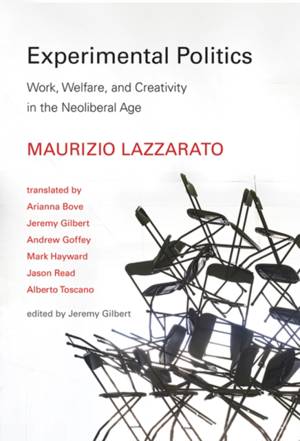
Experimental Politics
Maurizio Lazzarato
- Hardcover | Engels | Technologies of Lived Abstraction
- A celebrated theorist examines the conditions of work, employment, and unemployment in neoliberalism's flexible and precarious labor market. In Experi... Lees meer
€ 54,45€ 54,45 -
Broadband Infrastructure
Shailendra Jain, Mark Hayward, Sharad Kumar
- Hardcover | Engels
- Broadband Infrastructure: The Ultimate Guide to Understanding and Delivering OSS/BSS is a "how to" book for Internet infrastructure companies to help ... Lees meer
€ 245,45€ 245,45 -
Broadband Infrastructure
Shailendra Jain, Mark Hayward, Sharad Kumar
- Paperback | Engels
- Broadband Infrastructure: The Ultimate Guide to Understanding and Delivering OSS/BSS is a "how to" book for Internet infrastructure companies to help ... Lees meer
€ 195,95€ 195,95 -
Overcoming Distressing Voices, 2nd Edition
Mark Hayward, Clara Strauss, David Kingdon
- Paperback | Engels
- Practical help for managing distressing voice hearing experiences Have you ever heard someone talking to you, but when you turned around no one was th... Lees meer
€ 18,45€ 18,45 -
The Beatles: On Camera, Off Guard
Mark Hayward
- Hardcover
- It perhaps seems impossible that any images of the Beatles remain unseen, but this fascinating book accompanied by a DVD of rare 8mm footage provides ... Lees meer
€ 42,45€ 42,45 -
Overcoming Distressing Voices, 2nd Edition
Mark Hayward, David Kingdon, Clara Strauss
- E-book | Engels
- Practical help for managing distressing voice hearing experiences Have you ever heard someone talking to you, but when you turned around no one was th... Lees meer
€ 3,99€ 3,99 -
An Introduction to Self-help for Distressing Voices
Cassie Hazell, Mark Hayward, Kingdon David Strauss Clara
- Paperback | Engels | Introduction to Coping
- An invaluable guide to dealing with distressing voices from leading experts Hearing voices can be highly distressing and impact our health, well-being... Lees meer
€ 28,95€ 28,95 -
An Introduction to Self-help for Distressing Voices
Cassie Hazell, Mark Hayward, Clara Strauss, David Kingdon
- E-book | Engels | An Introduction to Coping series
- An invaluable guide to dealing with distressing voices from leading experts Hearing voices can be highly distressing and impact our health, well-being... Lees meer
€ 7,99€ 7,99 -
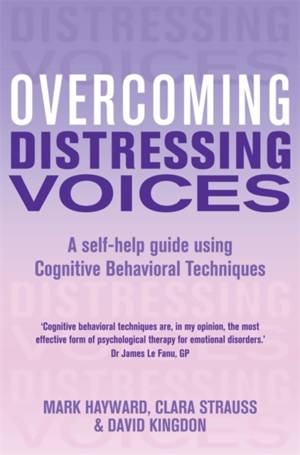
Overcoming Distressing Voices
Mark Hayward, David Kingdon, Clara Strauss
- Paperback
- An authoritative self-help guide to coping with hearing voices using cognitive behavioural therapy from the bestselling Overcoming series Lees meer
€ 15,45€ 15,45 -
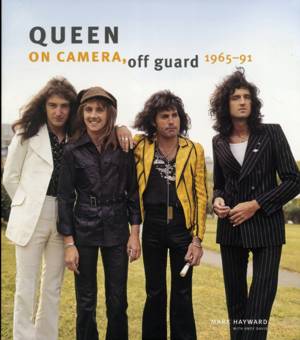
Queen: On Camera, Off Guard
Mark Hayward
- Hardcover
- Queen: On Camera, Off Guard includes a fantastic selection of rare images from one of the world's best-loved supergroups - featuring pictures from 196... Lees meer
€ 34,95€ 34,95 -
Identity and Industry
Mark Hayward
- Hardcover | Engels
- In 1947, grocer Johnny Lombardi went on air for the first time to share the sounds of sunny Italy with the radio listeners of Toronto. Meanwhile, in c... Lees meer
€ 177,45€ 177,45 -
Identity and Industry
Mark Hayward
- Paperback | Engels
- In 1947, grocer Johnny Lombardi went on air for the first time to share the sounds of "sunny Italy" with the radio listeners of Toronto. Meanwhile, in... Lees meer
€ 46,45€ 46,45 -
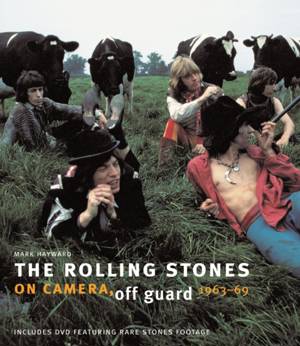
The Rolling Stones: On Camera, Off Guard
Mark Hayward
- Hardcover
- Still going strong after 40 years, The Rolling Stones have proved themselves to be the ultimate rock band. While we are familiar with images of the ba... Lees meer
€ 34,95€ 34,95
13 van 13 resultaten getoond